Continuing the discussion from Certificate on Aggregate sandbox-server expired:
Hi there,
after the certificate issue with the sandbox aggregate server was resolved (thanks a lot!), I ran into another problem while following the "Getting started with ODK" guide.
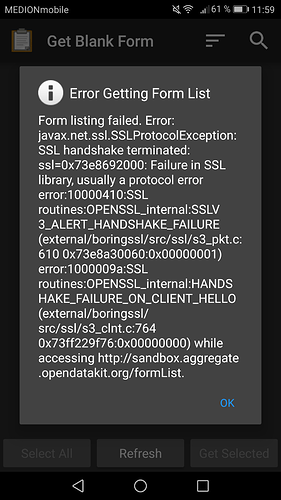
When I try to download the list of forms from the server to the ODK Collect app I get the following error message with an SSLProtocolException:
This happens for both http and https in the server-settings of the app & I'm using the latest version of the app.
My guess is that this is some kind of configuration problem, maybe app & sandbox server are trying to use different SSL/TLS protocol versions? Maybe something was changed while fixing the certificate problem?
Any help would be highly appreciated!
Yours,
Markus
I'm not sure this solution works for you or not, but it costs to test out.
Your device's date and time is automatic or manual? if it's manual or it's not equal to current date try to change it to automatic then try to get forms.
Date & time are set automatically and are correct.
Thanks for the suggestion though!
Sure! I'll review this 
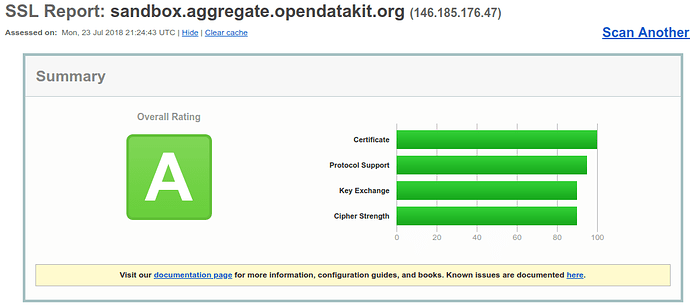
Anyway, what does it mean to fail the test you've linked, @yanokwa? I get this:
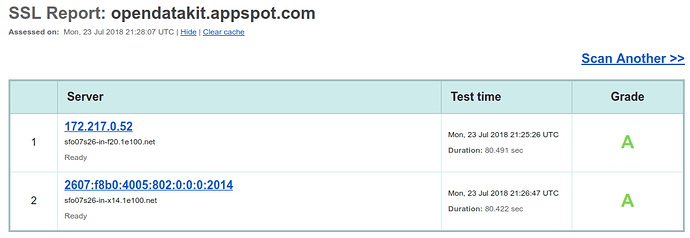
The second links gives me this:
The second report is a little confusing. App Engine responds to both IPv4 and IPv6. So you'll need to click on the 172.x link to see that report. And when you compare the appspot report with the sandbox, you'll see that they have different behavior for some versions of OpenSSL. I haven't looked closely, but I think the sandbox allows only newer ciphers...
1 Like
Hi, @MarkusSt! What Android version are you running?
Hey @ggalmazor, I'm running Android 7.0.
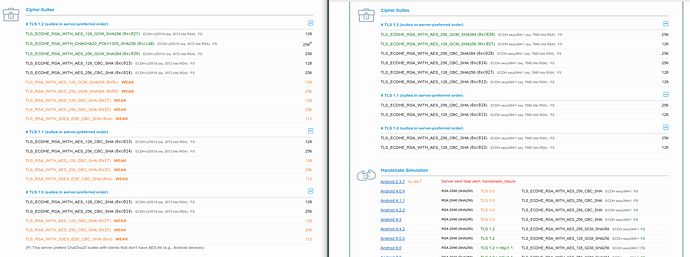
So, reporting back the differences I've seen:
Android 2.3.7
Android 7
I guess we should decide if we need to allow unsafe-ish TLS_RSA_WITH_AES_128_CBC_SHA in the sandbox or to support TLS_ECDHE_RSA_WITH_CHACHA20_POLY1305_SHA256 for h2.
Also interesting: the sanbox (right) doesn't support some other unsafe ciphers that are available in the AppEngine instance (left):
So, do I see it correctly that there shouldn't be any problems with Android 7.0? Or any version other than 2.3.7?
Maybe I'm confused because I'm no SSL expert myself, but it does seem so...
So, I've learned that the cipher suite is defined in nginx and we can activate any cipher we want. I could take the list of ciphers supported by opendatakit.appspot.com and activate them, but that would include some considered as weak. What do you think, @yanokwa?
Update: This OWASP table defines the "Broad Compatibility" openssl cipher suite for what I think we could need https://www.owasp.org/index.php/TLS_Cipher_String_Cheat_Sheet
If GAE supports those ciphers, I think they are safe enough, especially for a sandbox.
Since you are using nginx, it might be fastest just to copy the config that Central uses since that seems to work ok.
https://github.com/opendatakit/central/blob/HEAD/files/nginx/odk.conf.template
Alright so I've been testing with an Android 6.0 phone and an 8.0 phone, everything's working perfectly there.
Didn't find anyone else with version 7.0 yet.
But right now I'm assuming it's just related to my device so I'll keep working with a borrowed phone while I try to figure out what's wrong with mine.
Thanks for the help, I apprectiate it!
1 Like
I have an Android 7 device and the current config was causing me problems.
@ggalmazor I've changed commented out the default configs and added the ones at https://github.com/opendatakit/central/blob/HEAD/files/nginx/odk.conf.template and restarted nginx. Seems to work great with Android 7 now.
2 Likes
Thanks, @yanokwa! Yesterday I got distracted after our meeting and I forgot to do it, sorry!
Works perfectly now, thank you so very much!